Cloud Deployment Firm Vercel Breached: Essential Guide to Secrets Rotation and Security Recovery
Cloud Deployment Firm Vercel Breached: Essential Guide to Secrets Rotation and Security Recovery
The cybersecurity landscape has been rocked by the recent announcement that Vercel, a titan in the cloud deployment and frontend infrastructure space, has experienced a security incident. Known primarily as the creator and maintainer of Next.js, Vercel is the backbone for millions of modern web applications. When a platform of this magnitude reports a breach, the ripples are felt across the entire DevOps and software development community. Vercel has officially advised its users to perform a secrets rotation, a critical security procedure designed to invalidate potentially compromised credentials and restore the integrity of the development pipeline.
In this comprehensive guide, we will break down the specifics of the Vercel breach, analyze the technical implications for developers, and provide a step-by-step roadmap for securing your infrastructure. Whether you are a solo developer or an enterprise CTO, understanding the nuances of this incident is vital for maintaining a resilient cloud presence.
Understanding the Vercel Security Breach: What We Know So Far
Vercel’s rise to dominance in the "Frontend Cloud" market makes it a high-value target for threat actors. While the company maintains rigorous security standards, no platform is entirely immune to sophisticated attacks. The recent breach reportedly involved unauthorized access that could potentially expose sensitive environment variables—often referred to as "secrets"—associated with user projects. These secrets typically include API keys, database connection strings, and authentication tokens that allow applications to communicate with third-party services.
The incident highlights a growing trend in cybersecurity: Supply Chain Attacks. By targeting the deployment platform, attackers don't need to breach individual companies one by one. Instead, they can gain leverage over thousands of applications simultaneously. Vercel’s proactive communication regarding secrets rotation suggests that while their core infrastructure may be isolated, the "metadata" or the environment configurations managed by users may have been at risk.
What is Secrets Rotation and Why is it Critical?
In the context of modern web development, a "secret" is any sensitive piece of information used to authenticate a request. If an attacker gains access to your STRIPE_SECRET_KEY or your DATABASE_URL, they can effectively hijack your business operations or steal user data. Secrets rotation is the process of generating new credentials and revoking the old ones.
Vercel’s advice to rotate secrets is a defensive maneuver. By changing these values, you render any stolen data useless. If an attacker has a list of API keys stolen during the breach, those keys will fail to authenticate the moment you update them in the Vercel dashboard and redeploy your application. This is not just a "best practice"—in the wake of a breach, it is a mandatory recovery step to prevent unauthorized lateral movement within your cloud ecosystem.
| Feature/Aspect | Description |
|---|---|
| Incident Type | Unauthorized access to environment variable metadata. |
| Affected Platform | Vercel Cloud Deployment Services. |
| Primary Recommendation | Immediate rotation of all Environment Variables (Secrets). |
| Risk Level | High (Potential for data leakage and unauthorized API usage). |
| Recovery Steps | Update keys, redeploy apps, and audit access logs. |
Step-by-Step Guide: How to Rotate Your Vercel Secrets
Security experts recommend a systematic approach to rotating secrets to ensure that your live application does not experience downtime. Follow these steps to secure your Vercel projects:
1. Audit Your Current Environment Variables
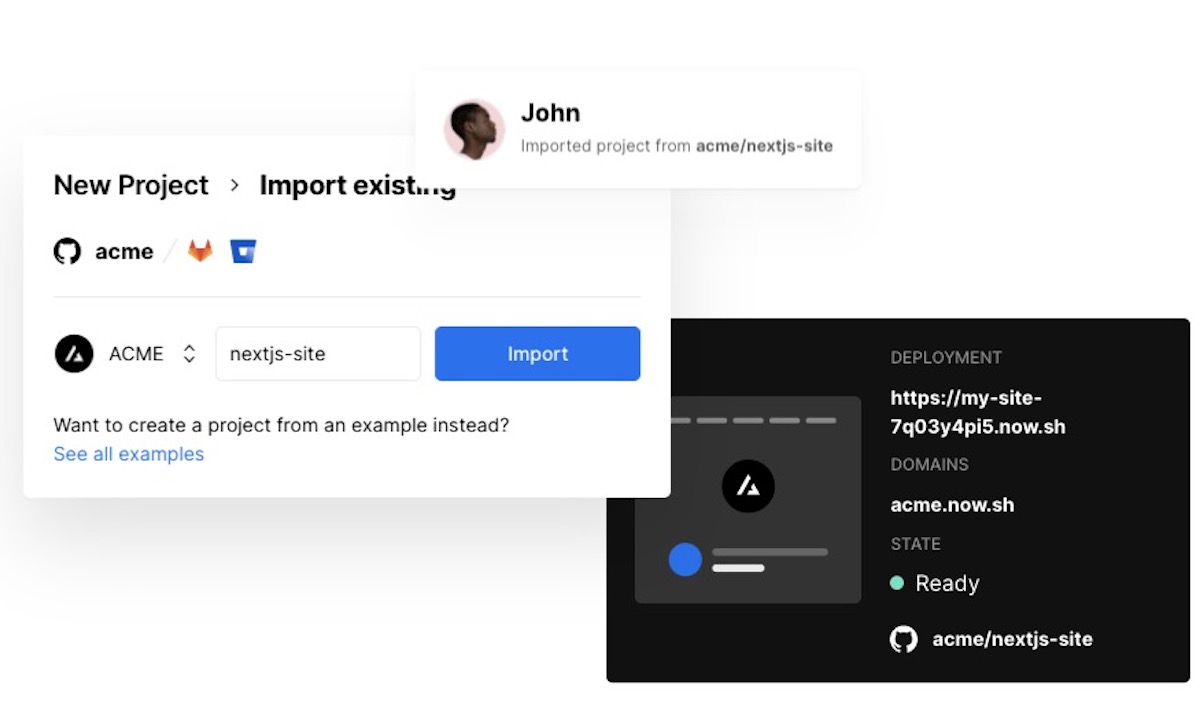
Log in to your Vercel Dashboard and navigate to each project's Settings > Environment Variables. Make a list of all external services integrated with your app (e.g., AWS, Supabase, SendGrid, OpenAI). You will need to log in to each of these external platforms to generate new keys.
2. Generate New Keys from Providers
Visit your third-party providers. For example, if you use Stripe, go to the Stripe Dashboard and "Roll" your API keys. Most modern platforms provide an option to "expire" the old key after a certain number of hours, giving you a window to update your code without breaking the production site.
3. Update Vercel Settings
Replace the old values in the Vercel Environment Variables section with the newly generated ones. Ensure you update the values for all environments: Production, Preview, and Development.
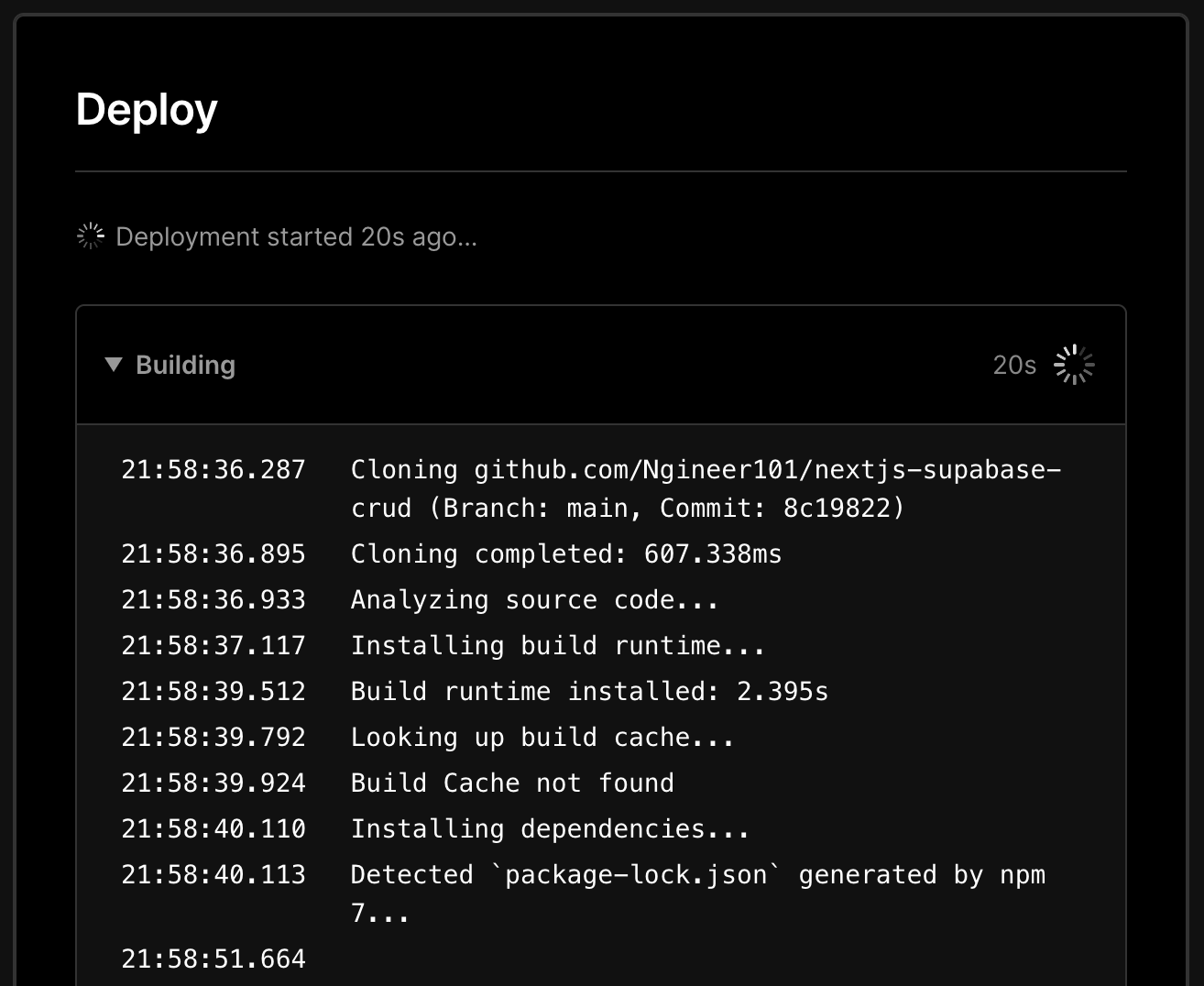
4. Trigger a Full Redeploy
Environment variables are injected during the build process. Simply updating the value in the dashboard is not enough. You must trigger a new deployment for the changes to take effect across your global edge network. You can do this via the Vercel CLI using vercel --prod or by pushing a new commit to your connected Git repository.
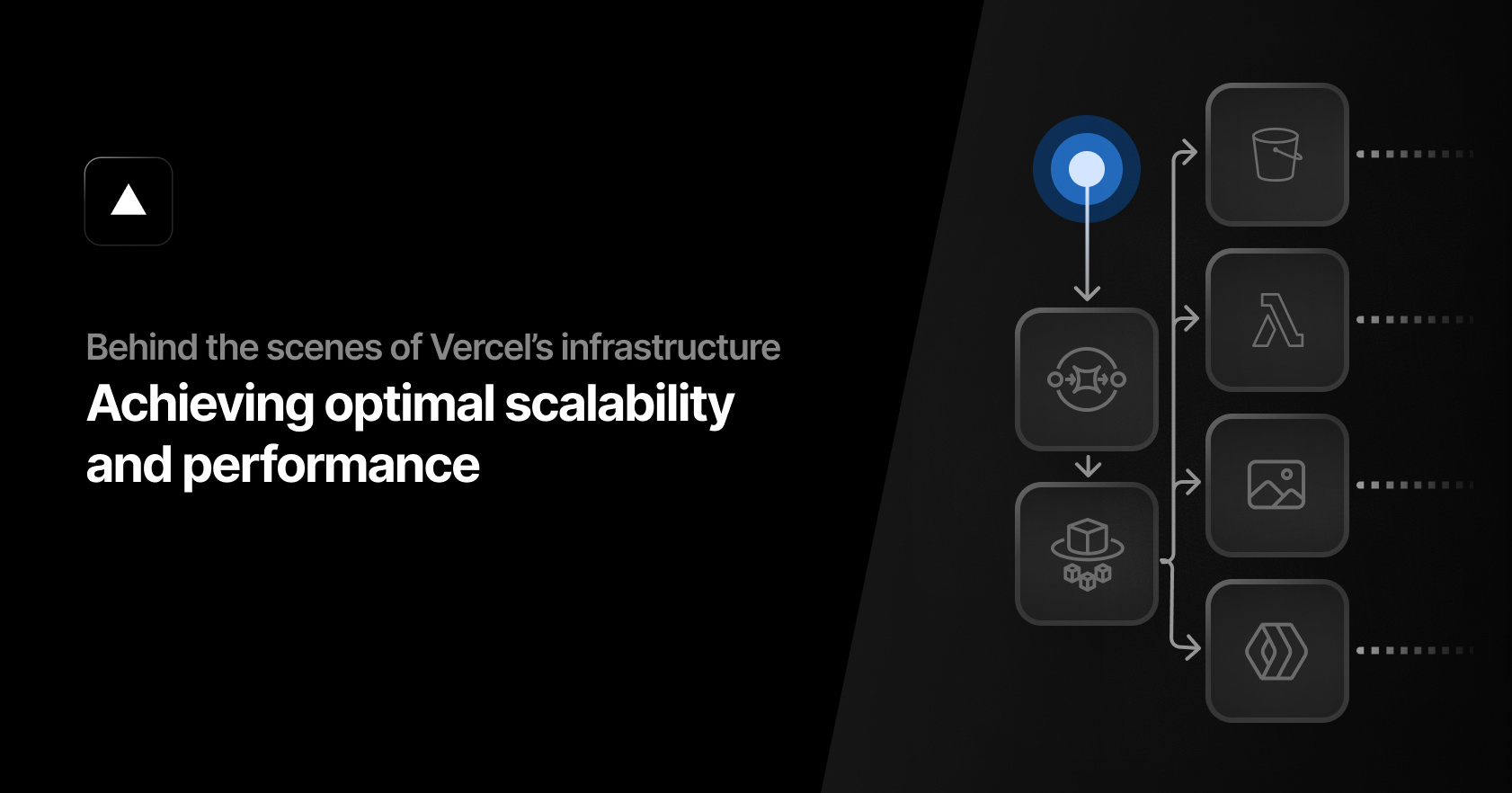
The Technical Impact: Why Manual Rotation Isn't Enough
For large organizations with hundreds of microservices, manual rotation is a logistical nightmare. This breach serves as a wake-up call for the adoption of Automated Secrets Management. Tools like HashiCorp Vault, AWS Secrets Manager, or Doppler can integrate with Vercel to programmatically update secrets. If you are still hard-coding secrets or manually pasting them into a UI, you are vulnerable to human error and delayed responses during a crisis.
Furthermore, developers must look beyond just environment variables. Consider your Vercel Personal Access Tokens (PATs). If these tokens were compromised, an attacker could deploy malicious code directly to your domains. Rotating your PATs in the Vercel Account Settings is just as important as rotating your database password.
Lessons for DevOps: Strengthening Your Cloud Security Posture
The Vercel incident provides several key takeaways for the modern DevOps professional. Security is not a static state but a continuous process of improvement and vigilance.
Implement the Principle of Least Privilege (PoLP)
Ensure that the API keys you provide to Vercel only have the permissions necessary for that specific application. For instance, an AWS S3 key should only have access to the specific bucket required for the project, rather than full administrative access to your entire AWS account.
Monitoring and Observability
Following a breach, it is vital to audit your logs. Vercel provides Runtime Logs and Deployment Logs. Look for unusual traffic patterns, unauthorized deployments, or API calls originating from unexpected IP addresses. Setting up automated alerts for "Secret Accessed" events can provide early warning signs of a compromise.
Shift-Left Security
Integrate security scanning into your local development environment. Use tools like git-secrets or trufflehog to ensure that no developer accidentally commits a secret to a Git repository, which is often how attackers gain their initial foothold in a deployment pipeline.
Communication and Transparency
If you are a service provider using Vercel, you have a responsibility to communicate with your own clients. Transparency builds trust. Explain the steps you have taken to rotate secrets and reassure them that their data remains protected. Vercel's prompt notification is a model for how companies should handle incident disclosure.
The Future of Frontend Cloud Security
As we move toward more "Serverless" and "Edge-first" architectures, the attack surface shifts. We are moving away from securing physical servers toward securing identities and configurations. The Vercel breach is a reminder that the configuration layer is the new perimeter. Future security trends will likely focus on "Short-lived Credentials"—tokens that expire in minutes or hours—reducing the window of opportunity for any potential thief.
Frequently Asked Questions (FAQ)
1. Is my Vercel site currently down because of the breach?
No, the breach does not necessarily cause downtime. However, your site may be vulnerable to data theft if your environment variables were compromised. You must rotate your secrets to ensure continued security, but the sites themselves remain operational unless you manually take them down.
2. Do I need to change my Vercel account password?
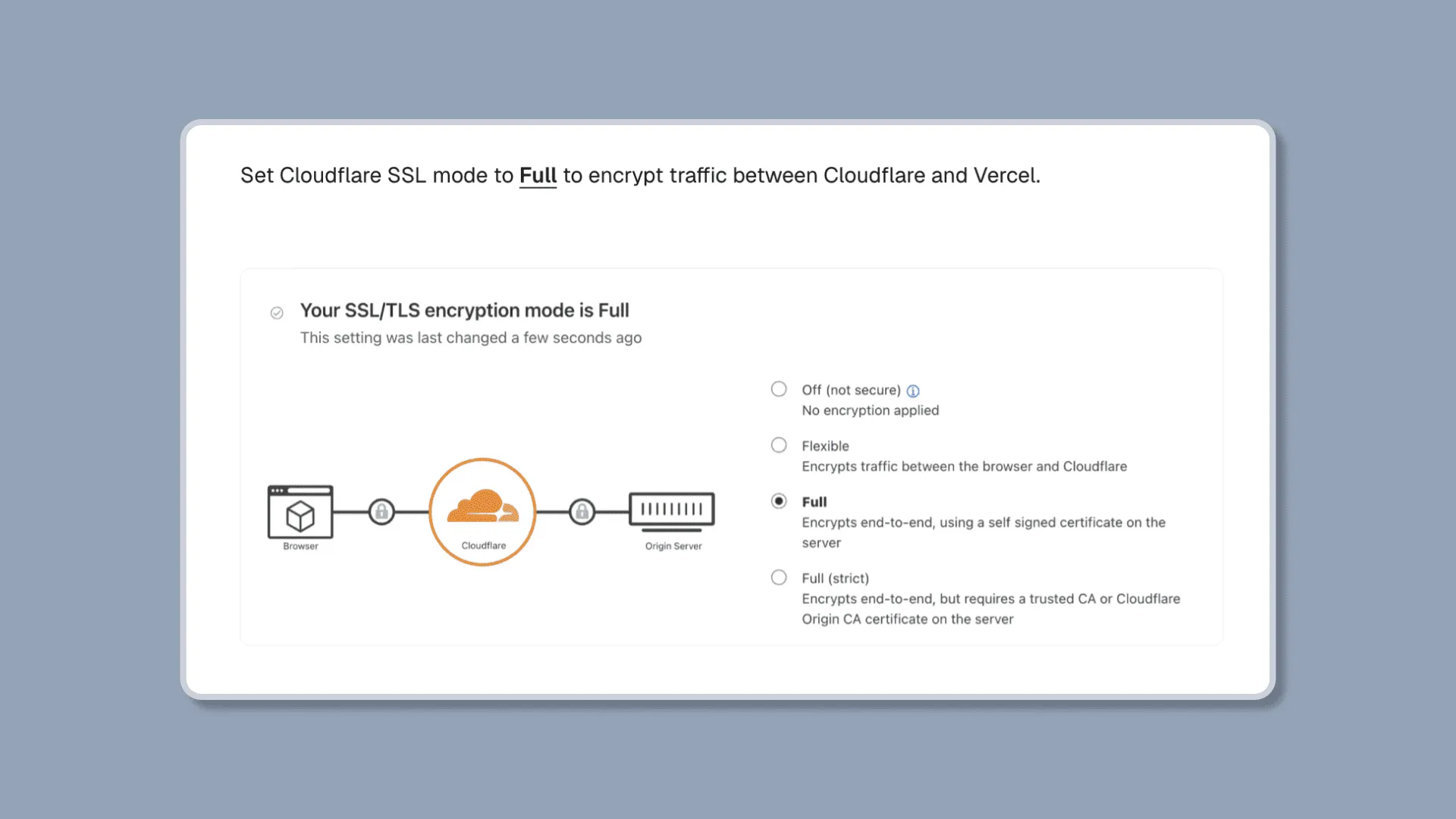
While the primary recommendation is secrets rotation for environment variables, it is always a best practice to update your account password and ensure that Multi-Factor Authentication (MFA) is enabled. If you use GitHub, GitLab, or Bitbucket to log in, ensure those accounts are also secured with MFA.
3. What happens if I don't rotate my secrets?
Failing to rotate secrets leaves a "backdoor" open. If an attacker harvested your API keys during the breach, they could continue to access your database, use your paid API credits (like OpenAI or Stripe), or exfiltrate sensitive user information indefinitely until those keys are revoked.
Conclusion: Moving Forward with a Security-First Mindset
The Vercel breach is a significant event in the cloud computing world, but it is also a manageable one. By following the advice to rotate secrets and auditing your deployment workflows, you can effectively neutralize the threat. This incident highlights the interdependency of modern web services; our security is only as strong as the platforms we build upon.
As the industry evolves, let this serve as a catalyst for better security hygiene. Move away from long-lived static secrets, embrace automated management tools, and always stay informed about the latest security updates from your infrastructure providers. Vercel remains a powerful and innovative platform, but like all tools, it must be used with a "Security-First" mindset to protect the digital assets of today and tomorrow.
Cloud deployment firm Vercel breached, advises secrets rotation
Cloud deployment firm Vercel breached, advises secrets rotation Wallpapers
Collection of cloud deployment firm vercel breached, advises secrets rotation wallpapers for your desktop and mobile devices.

Vibrant Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Wallpaper Nature
Experience the crisp clarity of this stunning cloud deployment firm vercel breached, advises secrets rotation image, available in high resolution for all your screens.

Serene Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Picture in 4K
Transform your screen with this vivid cloud deployment firm vercel breached, advises secrets rotation artwork, a true masterpiece of digital design.

Beautiful Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Moment Photography
Discover an amazing cloud deployment firm vercel breached, advises secrets rotation background image, ideal for personalizing your devices with vibrant colors and intricate designs.

Dynamic Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Capture Photography
This gorgeous cloud deployment firm vercel breached, advises secrets rotation photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Exquisite Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Landscape Art
This gorgeous cloud deployment firm vercel breached, advises secrets rotation photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Vibrant Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Photo Concept
Explore this high-quality cloud deployment firm vercel breached, advises secrets rotation image, perfect for enhancing your desktop or mobile wallpaper.

Vivid Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Scene in 4K
Transform your screen with this vivid cloud deployment firm vercel breached, advises secrets rotation artwork, a true masterpiece of digital design.
Lush Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Design in 4K
A captivating cloud deployment firm vercel breached, advises secrets rotation scene that brings tranquility and beauty to any device.

High-Quality Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Abstract Digital Art
Experience the crisp clarity of this stunning cloud deployment firm vercel breached, advises secrets rotation image, available in high resolution for all your screens.
Captivating Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Landscape Collection
Find inspiration with this unique cloud deployment firm vercel breached, advises secrets rotation illustration, crafted to provide a fresh look for your background.

Serene Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Scene for Desktop
Explore this high-quality cloud deployment firm vercel breached, advises secrets rotation image, perfect for enhancing your desktop or mobile wallpaper.

Lush Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Photo Nature
A captivating cloud deployment firm vercel breached, advises secrets rotation scene that brings tranquility and beauty to any device.
Crisp Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Picture Illustration
Immerse yourself in the stunning details of this beautiful cloud deployment firm vercel breached, advises secrets rotation wallpaper, designed for a captivating visual experience.

Amazing Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Background for Your Screen
Discover an amazing cloud deployment firm vercel breached, advises secrets rotation background image, ideal for personalizing your devices with vibrant colors and intricate designs.
Stunning Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Wallpaper Photography
Immerse yourself in the stunning details of this beautiful cloud deployment firm vercel breached, advises secrets rotation wallpaper, designed for a captivating visual experience.
Dynamic Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Landscape for Mobile
This gorgeous cloud deployment firm vercel breached, advises secrets rotation photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Spectacular Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Design in 4K
Find inspiration with this unique cloud deployment firm vercel breached, advises secrets rotation illustration, crafted to provide a fresh look for your background.

Detailed Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation View Illustration
Discover an amazing cloud deployment firm vercel breached, advises secrets rotation background image, ideal for personalizing your devices with vibrant colors and intricate designs.

Amazing Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Design Digital Art
Transform your screen with this vivid cloud deployment firm vercel breached, advises secrets rotation artwork, a true masterpiece of digital design.
Mesmerizing Cloud Deployment Firm Vercel Breached, Advises Secrets Rotation Image for Your Screen
Explore this high-quality cloud deployment firm vercel breached, advises secrets rotation image, perfect for enhancing your desktop or mobile wallpaper.
Download these cloud deployment firm vercel breached, advises secrets rotation wallpapers for free and use them on your desktop or mobile devices.